Cyber SecurityModern Tools for Penetration Assessment Testing
The relentless advancement of technology has led to the parallel evolution of cybersecurity threats. These threats necessitate continuous improvement of cybersecurity defenses. One of the pillars of these defenses is penetration testing, commonly referred to as penetration assessment or pen testing. Penetration testing entails the simulation of cyber-attacks on your system to discover vulnerabilities that can potentially be exploited by cybercriminals. This article will explore some of the modern tools used for penetration testing in our rapidly changing technological world.
1. Metasploit
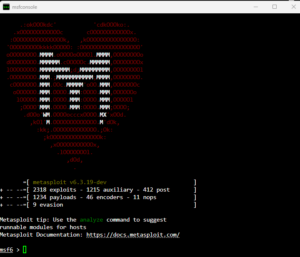
Figure 1: Metasploit Framework
One of the most reliable tools for penetration testing, Metasploit, is a potent, open-source framework that allows for the development, testing, and execution of exploit codes. Developed by Rapid7, Metasploit facilitates vulnerability discovery, exploitation, and verification. It provides a centralized repository of exploits and allows users to create their modules, making it a highly versatile tool for both experts and beginner testers.
2. Wireshark
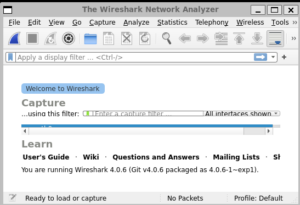
Figure 2: Wireshark
Wireshark is a highly acclaimed network protocol analyzer that captures and interacts with network traffic in real-time. It enables testers to examine numerous protocols, perform live capture, and offline analysis. Wireshark’s extensive inspection capabilities make it an indispensable tool for network troubleshooting and understanding the challenges associated with network protocol operations.
3. Nessus

Figure 3: Nessus
Regarded as the standard for vulnerability assessments, Nessus is an all-inclusive vulnerability scanner by Tenable Network Security. With over 70,000 plugins, Nessus checks for network-based and host-based vulnerabilities, configuration issues, among others. It can be deployed on various platforms, offering extensive and diverse network monitoring capabilities.
4. Burp Suite
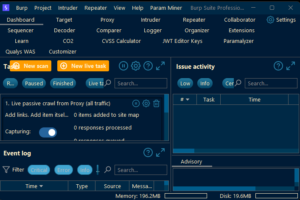
Figure 4: BurpSuite Pro
Designed specifically for web application security testing, Burp Suite is a trusted tool with a multitude of features. These features range from crawling web applications and analyzing web traffic to manipulating and forwarding network requests. The suite includes an intruder, repeater, sequencer, and more, assisting in identifying and exploiting vulnerabilities.
5. Nmap
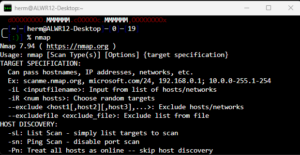
Figure 5: NMAP
Also known as Network Mapper, Nmap is a flexible, robust, and portable tool used for network discovery and security auditing. It uses raw IP packets to identify available hosts on the network, the services these hosts offer, the operating systems they run, and more.
6. Aircrack-ng
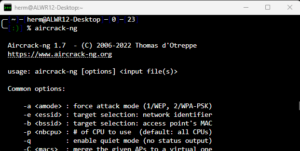
Figure 6: Aircrack-Ng
Designed for assessing Wi-Fi network security, Aircrack-ng is a complete suite of tools. It is used for packet sniffing, detecting attacks, and cracking WEP and WPA PSK keys. Aircrack-ng is a must-have tool for penetration testers addressing wireless network vulnerabilities.
7. OWASP ZAP
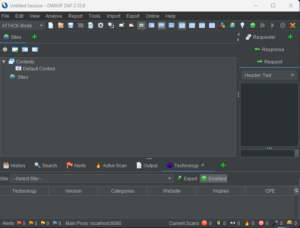
Figure 7: OWASP ZAPP
The Zed Attack Proxy (ZAP) is an open-source web application security scanner developed by OWASP (Open Web Application Security Project). It’s a highly configurable tool and can be used by people with a wide range of security experience. With its automated scanner, advanced fuzzing techniques, and a traditional and AJAX spider, ZAP is one of the world’s most popular free security tools for identifying security vulnerabilities in web applications.
8. SQLmap
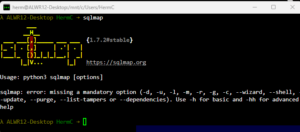
Figure 8: SQLmap
An open-source penetration testing tool, SQLmap automates the process of detecting and exploiting SQL injection flaws. With a potent detection engine, many unique features for the ultimate penetration tester, and broad database support, it is an invaluable tool for penetration testing against SQL injection vulnerability.
9. Kali Linux
Figure 9: Kali Linux
Kali Linux is a Debian-based Linux distribution equipped with hundreds of penetration testing and security auditing tools. Covering aspects from information gathering to vulnerability analysis, wireless attacks, and reverse engineering, Kali Linux is a comprehensive platform for any penetration tester.
The dynamism of technological development means that cybersecurity must continuously adapt and evolve to counter new threats and challenges. Modern penetration testing tools provide an essential resource in this continuous effort, highlighting vulnerabilities before malicious actors can exploit them.
In the ever-evolving world of cybersecurity, penetration testing is a crucial preemptive measure to protect your systems and data. Each of these tools offers unique capabilities and strengths, contributing to a holistic, proactive approach to cybersecurity. Getting acquainted with them and understanding how they can be applied to test your system’s robustness is the first step towards developing a sturdy security framework.
Don’t become the next victim of a breach, schedule your penetration test today!
Introducing Winmill’s Penetration Testing Stream
We’re excited to announce our latest offering: the Penetration Testing Stream subscription. Designed to fortify your organization’s cybersecurity posture, the Penetration Testing Stream provides continuous assurance. Whether you’re safeguarding critical infrastructure or ensuring compliance with industry standards, our expert team delivers fast, comprehensive testing to help you mitigate risks effectively.
Contact us today and discover how Winmill’s Penetration Testing Stream can provide continuous assurance for your business.
Get a Quote on a Penetration Testing Stream Subscription
1501 Broadway STE 12060
New York, NY 10036-5601
